Overview
Authelia is an open-source authentication service that allows you to place a portal between end users on the internet and self-hosted services on your server.
You can require one factor (username+password) or two factor authentication for any such user before allowing them to access a specific service on your domain.
This guide will walk through a standard installation of Authelia for
example.com, using auth.example.com as Authelia's authentication domain and
teddit.example.com as the website we want to protect behind the authentication
portal.
Prerequisites
This guide assumes you have the following already set-up:
- A registered domain with DNS pointing to your server.
- A subdomain for Authelia (
auth.example.com) and a subdomain to protect via Authelia (app.example.com). - A working Nginx web server.
- Docker and docker-compose installed.
Installation
This guide will walk through each installation step one-by-one, starting with the container and finishing by cleaning up external access via an Nginx reverse proxy.
Docker-Compose
To start, create a directory for Authelia and create a docker-compose.yml
file.
Within this file, paste the following content. If you prefer a different local
port, modify the port on the left side of the colon on the 9091:9091 line. Be
sure to modify the TZ variable to your timezone.
version: "3.3"
services:
authelia:
image: authelia/authelia
container_name: authelia
volumes:
- ./config:/config
ports:
- 9091:9091
environment:
- TZ=America/Chicago
Start the container with docker-compose:
After the first start, the container will automatically exit and require you to modify the app's configuration files before continuing. Read on to learn more.
Authelia Configuration
To configure Authelia before we restart the container, we need to open the
config directory and modify the files. Start by editing the
configuration.yml file, where all of Authelia's settings are stored.
My personal preference is to copy the original configuration file to a backup file and edit a fresh copy.
Within the blank configuration.yml file, paste the following information. You
will need to make quite a few updates, so be sure to read each line carefully
and modify as necessary.
The major required changes are:
- Any instances of
example.comshould be replaced by your domain. jwt_secret- Use thepwgen 40 1command to generate a secret for yourself.access_control- Set the Authelia domain to bypass here, as well as any subdomains you want to protect.session>secret- Use thepwgen 40 1command to generate a secret for yourself.regulation- Set the variables here to restrict login attempts and bans.storage>encryption_key- Use thepwgen 40 1command to generate a secret for yourself.smtp- If you have access to an SMTP service, set up the information here to active outgoing emails.
# yamllint disable rule:comments-indentation
---
###############################################################################
# Authelia Configuration #
###############################################################################
theme: dark
jwt_secret: aiS5iedaiv6eeVaideeLeich5roo6ohvaf3Vee1a # pwgen 40 1
default_redirection_url: https://example.com
server:
host: 0.0.0.0
port: 9091
path: ""
read_buffer_size: 4096
write_buffer_size: 4096
enable_pprof: false
enable_expvars: false
disable_healthcheck: false
tls:
key: ""
certificate: ""
log:
level: debug
totp:
issuer: example.com
period: 30
skew: 1
authentication_backend:
disable_reset_password: false
refresh_interval: 5m
file:
path: /config/users_database.yml
password:
algorithm: argon2id
iterations: 1
key_length: 32
salt_length: 16
memory: 1024
parallelism: 8
access_control:
default_policy: deny
rules:
- domain:
- "auth.example.com"
policy: bypass
- domain: "teddit.example.com"
policy: one_factor
session:
name: authelia_session
secret: aiS5iedaiv6eeVaideeLeich5roo6ohvaf3Vee1a # pwgen 40 1
expiration: 3600
inactivity: 300
domain: example.com
regulation:
max_retries: 5
find_time: 10m
ban_time: 12h
storage:
local:
path: /config/db.sqlite3
encryption_key: aiS5iedaiv6eeVaideeLeich5roo6ohvaf3Vee1a # pwgen 40 1
notifier:
disable_startup_check: true
smtp:
username: [email protected]
password: password
host: smtp.example.com
port: 465
sender: [email protected]
identifier: example.com
subject: "[Authelia] {title}"
startup_check_address: [email protected]
disable_require_tls: false
disable_html_emails: true
tls:
skip_verify: false
minimum_version: TLS1.2
Authelia Users
Next, create the users file for authentication.
Within the file, you will need to create an entry for each user that needs
access to Authelia. The my_username entry will be the username used on the
login page.
To generate the password, go to Argon2 Hash Generator,
generate a random salt, and make sure the rest of the settings match the
authentication_backend section of configuration.yml file.
users:
my_username:
displayname: "My User"
# Generated at https://argon2.online/ -- match the settings in
# the `authentication_backend` section of configuration.yml
password: ""
email: [email protected]
groups:
- admins
- dev
Once the app is configured, restart the container from scratch.
&&
Nginx: Authelia Domain
Once the container is running and configured, the final step is to configure external access to the server via Nginx reverse proxy.
Start by creating the Authelia domain.
Within this file, paste the following information and be sure to update
example.com to your domain. Make sure the $upstream_authelia variable
matches the location of your Authelia container.
server {
if ($host ~ ^[^.]+\.example\.com$) {
301 ;
}
[::]:80;
80;
auth.example.com;
404;
}
server {
[::]:443 ssl http2;
443 ssl http2;
auth.example.com;
/var/log/nginx/auth.access.log;
/var/log/nginx/auth.error.log;
/etc/letsencrypt/live/example.com/fullchain.pem;
/etc/letsencrypt/live/example.com/privkey.pem;
include /etc/letsencrypt/options-ssl-nginx.conf;
/etc/letsencrypt/ssl-dhparams.pem;
location / {
$upstream_authelia ;
$upstream_authelia;
128k;
error timeout invalid_header http_500 http_502 http_503;
5m;
360;
360;
360;
Host $host;
X-Real-IP $remote_addr;
X-Forwarded-For $proxy_add_x_forwarded_for;
X-Forwarded-Proto $scheme;
X-Forwarded-Host $http_host;
X-Forwarded-Uri $request_uri;
X-Forwarded-Ssl on;
http:// $scheme://;
1.1;
Connection "";
$cookie_session;
$cookie_session;
64 256k;
}
}
Next, symlink the file and restart Nginx. If there are errors, be sure to resolve those before moving on.
Nginx: Protected Domain(s)
Now that Authelia is accessible externally, you need to configure the domain you
intend to protect with Authelia. In this example, I'm protecting
teddit.example.com.
Similar to the process above, paste the content and update the relevant variables.
server {
if ($host ~ ^[^.]+\.example\.com$) {
301 ;
}
[::]:80;
80;
teddit.example.com;
404;
}
server {
[::]:443 ssl http2;
443 ssl http2;
teddit.example.com;
/var/log/nginx/teddit.access.log;
/var/log/nginx/teddit.error.log;
X-Content-Type-Options "nosniff";
X-XSS-Protection "1; mode=block";
X-Frame-Options "DENY";
Strict-Transport-Security "max-age=63072000; includeSubDomains";
Referrer-Policy "no-referrer";
/etc/letsencrypt/live/example.com/fullchain.pem;
/etc/letsencrypt/live/example.com/privkey.pem;
include /etc/letsencrypt/options-ssl-nginx.conf;
/etc/letsencrypt/ssl-dhparams.pem;
location /authelia {
internal;
$upstream_authelia ;
off;
$upstream_authelia;
Content-Length "";
error timeout invalid_header http_500 http_502 http_503;
128k;
Host $host;
X-Original-URL $scheme://$http_host$request_uri;
X-Real-IP $remote_addr;
X-Forwarded-For $remote_addr;
X-Forwarded-Proto $scheme;
X-Forwarded-Host $http_host;
X-Forwarded-Uri $request_uri;
X-Forwarded-Ssl on;
http:// $scheme://;
1.1;
Connection "";
$cookie_session;
$cookie_session;
4 32k;
5m;
240;
240;
240;
}
location / {
$upstream_teddit ;
$upstream_teddit;
/authelia;
$target_url ;
$user $upstream_http_remote_user;
$email $upstream_http_remote_email;
$groups $upstream_http_remote_groups;
Remote-User $user;
Remote-Email $email;
Remote-Groups $groups;
401 =302 ;
128k;
error timeout invalid_header http_500 http_502 http_503;
5m;
360;
360;
360;
Host $host;
Upgrade $http_upgrade;
Connection upgrade;
Accept-Encoding gzip;
X-Real-IP $remote_addr;
X-Forwarded-For $proxy_add_x_forwarded_for;
X-Forwarded-Proto $scheme;
X-Forwarded-Host $http_host;
X-Forwarded-Uri $request_uri;
X-Forwarded-Ssl on;
http:// $scheme://;
1.1;
Connection "";
$cookie_session;
$cookie_session;
64 256k;
}
}
Same as before, symlink the file and restart Nginx.
Results
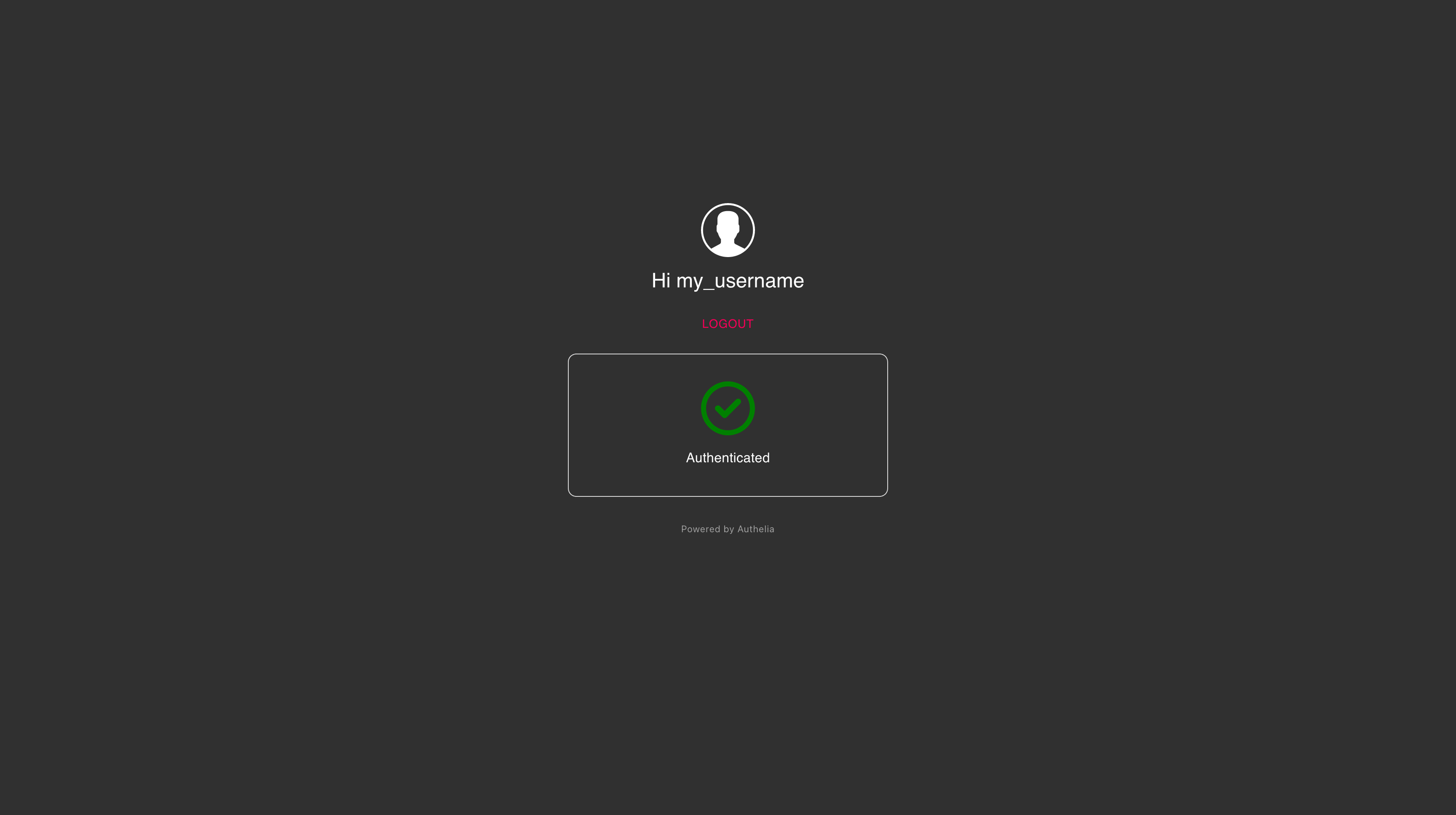
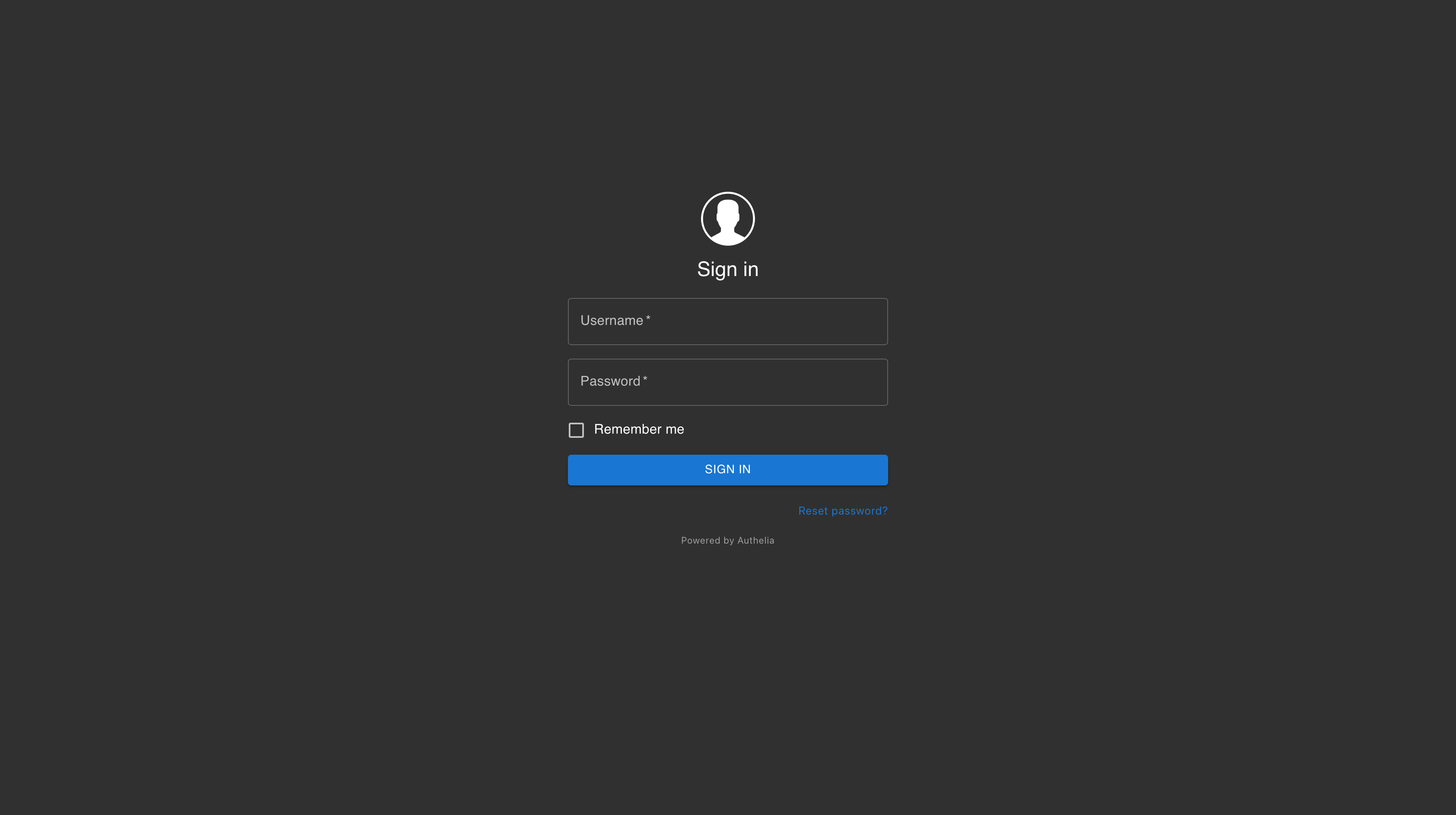
When visiting the protected domain, you will now be redirected to your authentication domain and presented with the Authelia login portal.
Once you've successfully authenticated, you can visit your authentication domain directly and see that you're currently authenticated to any domain protected by Authelia.